Zero-trust security “is not one single product that one can purchase off the shelf,” a NIST scientist observes. But underlying zero trust’s many component parts are a few critical elements, including identity and automation.
By Brad D. Williams
The patch secures a zero-day vulnerability disclosed last month and is just one of four vulnerabilities being actively exploited in Pulse Connect Secure.
By Brad D. Williams
“We are working with each agency to validate whether an intrusion has occurred and will offer incident response support accordingly,” CISA’s deputy executive assistant director told Breaking Defense.
By Brad D. Williams
“My hope is that we can create this structure… to get an early warning system,” the Senate Intel Committee chair said. “Voluntary sharing is no longer effective.”
By Brad D. Williams
Threat actors are targeting one newly discovered and three previously known vulnerabilities in Pulse Connect Secure enterprise VPNs, according to a CISA emergency directive and alert, as well as blog posts by FireEye and Ivanti. “There is no indication the identified backdoors were introduced through a supply chain compromise of the company’s network or software deployment process,” FireEye noted.
By Brad D. Williams
“If you try to life-extend a weapon system that was built before the invention of the Internet, and then turn around and ask me why it’s not cyber-secure — I don’t know how,” Adm. Charles Richard told SASC today.
By Theresa Hitchens
“The innovations… and the lessons learned from these responses will be used to improve future unified, whole of government responses to significant cyber incidents,” the White House says.
By Brad D. Williams
The White House Executive Order comes on the same day that CISA and CNMF issue SolarWinds-related malware analysis and NSA-CISA-FBI issue a joint advisory warning of ongoing SVR exploitation of known vulnerabilities in common products.
By Brad D. Williams
SolarWinds threat actor reportedly accessed DHS emails and DoE schedules. Cyberespionage campaigns are “the types of things we should expect [Russia] to do,” one cybersecurity expert observed. “I’m not arguing we shouldn’t have a response. We should respond. …My only argument is that we should not overact.”
By Brad D. Williams
“We should understand what our adversaries are doing,” Gen. Nakasone told Congress. “They are no longer launching attacks from different parts in the world. They understand that they can come into the US, use our infrastructure, and there’s a blind spot for us not being able to see them.”
By Brad D. Williams
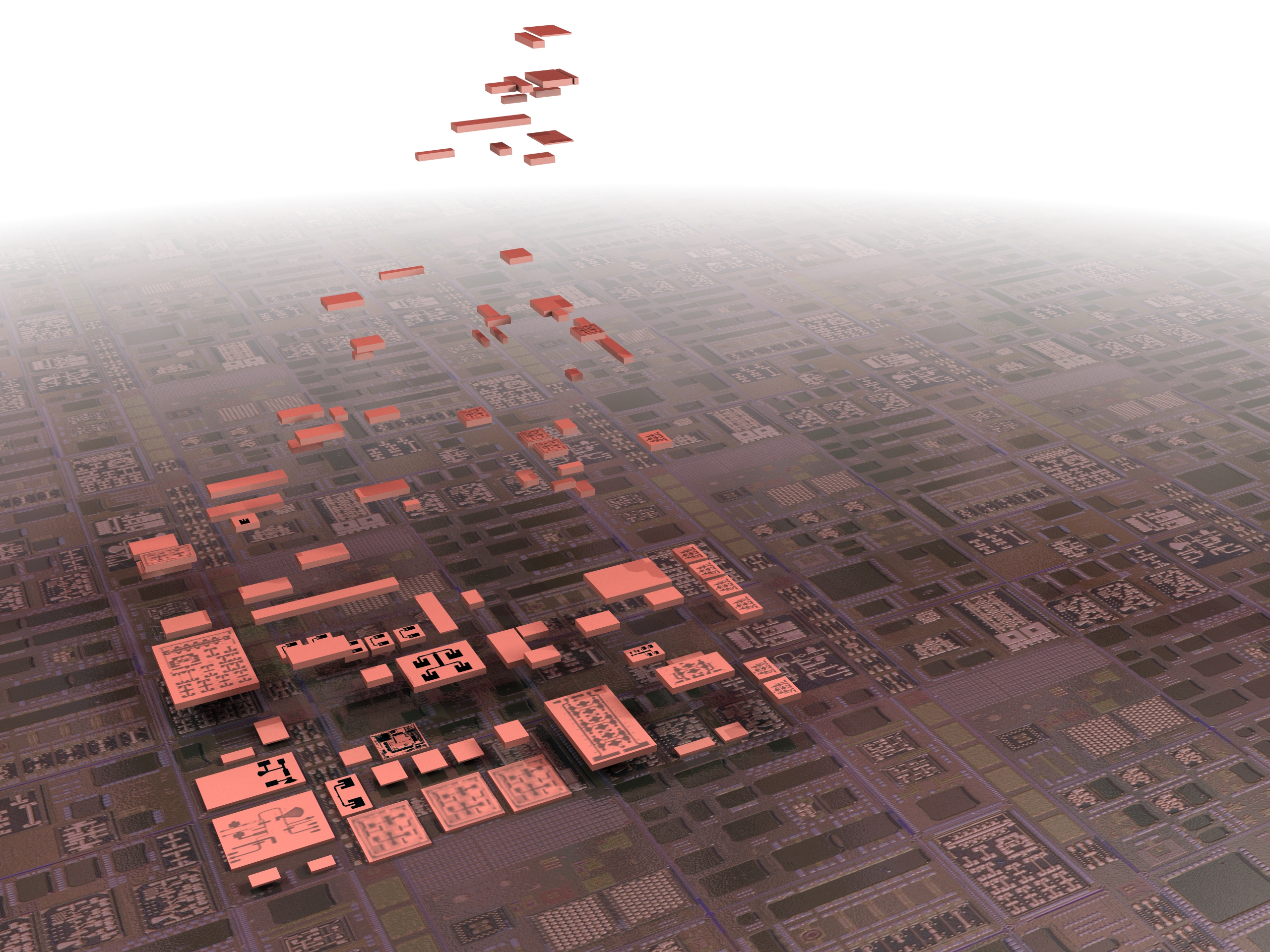
Corell spoke on information and communications tech (ICT) supply chain risks on the same day DARPA and Intel announced a three-year partnership to develop and domestically manufacture new semiconductors for DoD applications.
By Brad D. Williams
Only after months of investigation by nearly 100 highly skilled digital forensics experts did FireEye discover the malicious “implant” in the most unlikely place. We break it all down in plain language.
By Brad D. Williams
Three experts gave us exclusive in-depth insights into the administration’s potential menu of retaliatory options, along with U.S. cyber strategic, policy, and operations considerations.
By Brad D. Williams
As the government investigation continues, security firm FireEye published details of newly discovered backdoor, SUNSHUTTLE, which has “possible connection” to the SolarWinds hack.
By Brad D. Williams