
“I’ve never gotten a briefing from the Space Development Agency,” Roper said, “so I don’t know what their plan, I don’t know what they’re intending.”
By Theresa Hitchens
Four military installations, yet to be named, will host experiments in VR training, tracking supplies in “smart warehouses,” and – most importantly – sharing scarce spectrum.
By Sydney J. Freedberg Jr.
The Air Force sees the New Mexico training environment as eventually becoming a cyber training range for the entire Defense Department.
By Theresa Hitchens
“What I want to bet on is the ability of the United States and our Western allies to out-innovate adversaries,” says Mike Griffin, undersecretary of Defense for research and engineering.
By Theresa Hitchens
How do you find hundreds of vulnerabilities hidden in millions of lines of firmware code?
By Sydney J. Freedberg Jr.
“This is such a data-rich world that the person who can command that data first is the one who’s gonna have a real advantage.”
By Theresa Hitchens“Autonomy may look like an Achilles’ heel, and in a lot of ways it is” – but for both sides, DTRA’s Nick Wager said. “I think that’s as much opportunity as that is vulnerability. We are good at this… and we can be better than the threat.”
By Sydney J. Freedberg Jr.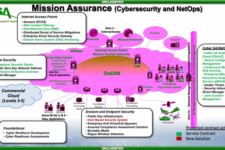
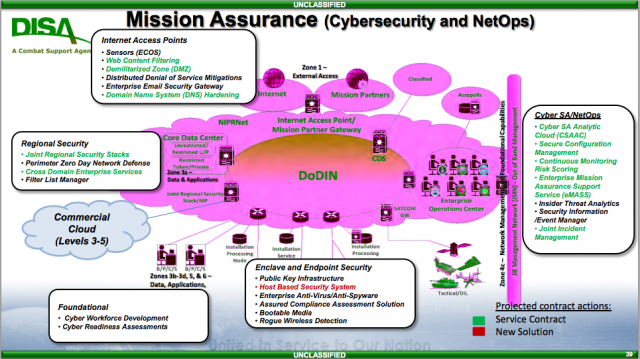
“We’re going to turn that off unless you secured that properly. Whoa! That’s a very different mindset,” Col. Straub told me. “The availability of the network versus the defense of the network, that’s something we’re trying to get commanders to think about.”
By Sydney J. Freedberg Jr.GEOINT: If you’re not an American citizen and you walk the halls of CIA headquarters and other U.S. intelligence agencies, lights flash alerting workers that a foreign national is walking by so that any secrets on their screens or desks can be protected from prying eyes. The main reason for this is that much intelligence is…
By Colin Clark















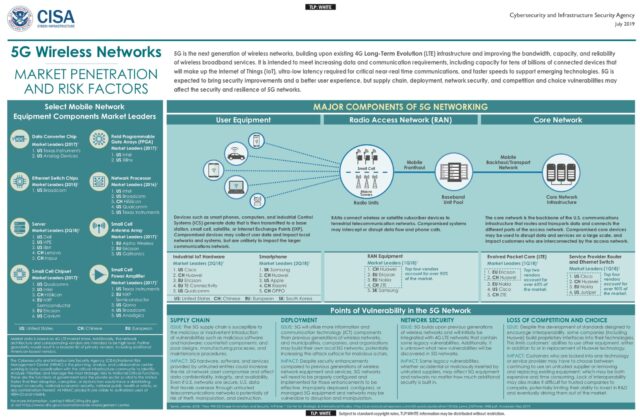











To protect the content of 5G transmissions, the Pentagon should accelerate development of mobile applications using end-to-end encryption. Today’s military radios or encrypted email only encrypt a message in transit. The message exists in an unencrypted form in the receiving server.
By Bryan Clark