

The directive was issued officially by the Israeli Cyber Directorate, but was initiated by the Israeli General Security Service (Shabak, known more commonly in English as Shin Bet), the highest authority on these issues. An earlier directive was voluntary. The new one requires Israeli companies to bar the Chinese materiel.
By Arie Egozi
Former intelligence officials told us they were worried about London’s decision to allow the Chinese giant’s technology on parts of its new 5G network. A vulnerability anywhere in the system, they argue, threatens security everywhere.
By Sydney J. Freedberg Jr.
“Security will be more important than speed in establishing a durable foundation for 5G’s future,” writes leading scholar Elsa Kania – and Washington must lead the way.
By Sydney J. Freedberg Jr.
“It’s not enough to develop and procure systems anymore. We’ve got to get in the business of of buying ideas and generating ideas,” says Air Force acquisition czar Will Roper.
By Theresa Hitchens
London is on the verge of a much-delayed and debated decision about allowing Huawei to build “non-core” components of its 5G network.
By Sydney J. Freedberg Jr.
Huawei founder Ren Zhengfei made a dramatic offer to let all comers license and modify his 5G technology. Making it secure would be a Herculean task.
By Sydney J. Freedberg Jr.
Nicholas Eftimiades, a former senior US senior intelligence officer, said the Trump Administration policy “is very surgical in its approach,” and will have only a “moderate impact” on allied countries.
By Theresa Hitchens
The coming network needed for autonomous vehicles, virtual reality, and the Internet of Things will also bring cybersecurity danger.
By Barry Rosenberg
“What I want to bet on is the ability of the United States and our Western allies to out-innovate adversaries,” says Mike Griffin, undersecretary of Defense for research and engineering.
By Theresa Hitchens
The secretary heads first to CENTCOM to hammer out the details of Operation Sentinel, a plan to monitor and protect shipping from Iran in Persian Gulf.
By Paul McLeary
How do you find hundreds of vulnerabilities hidden in millions of lines of firmware code?
By Sydney J. Freedberg Jr.
Trump’s declaration has to be translated into legal rules — by officials who don’t share his conciliatory stance.
By Sydney J. Freedberg Jr.
“This is such a data-rich world that the person who can command that data first is the one who’s gonna have a real advantage.”
By Theresa Hitchens





















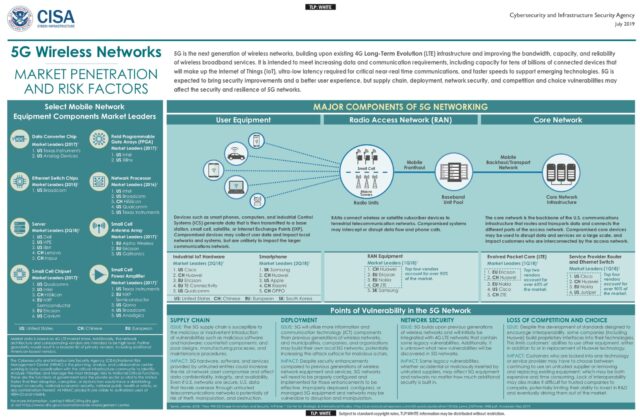







To protect the content of 5G transmissions, the Pentagon should accelerate development of mobile applications using end-to-end encryption. Today’s military radios or encrypted email only encrypt a message in transit. The message exists in an unencrypted form in the receiving server.
By Bryan Clark