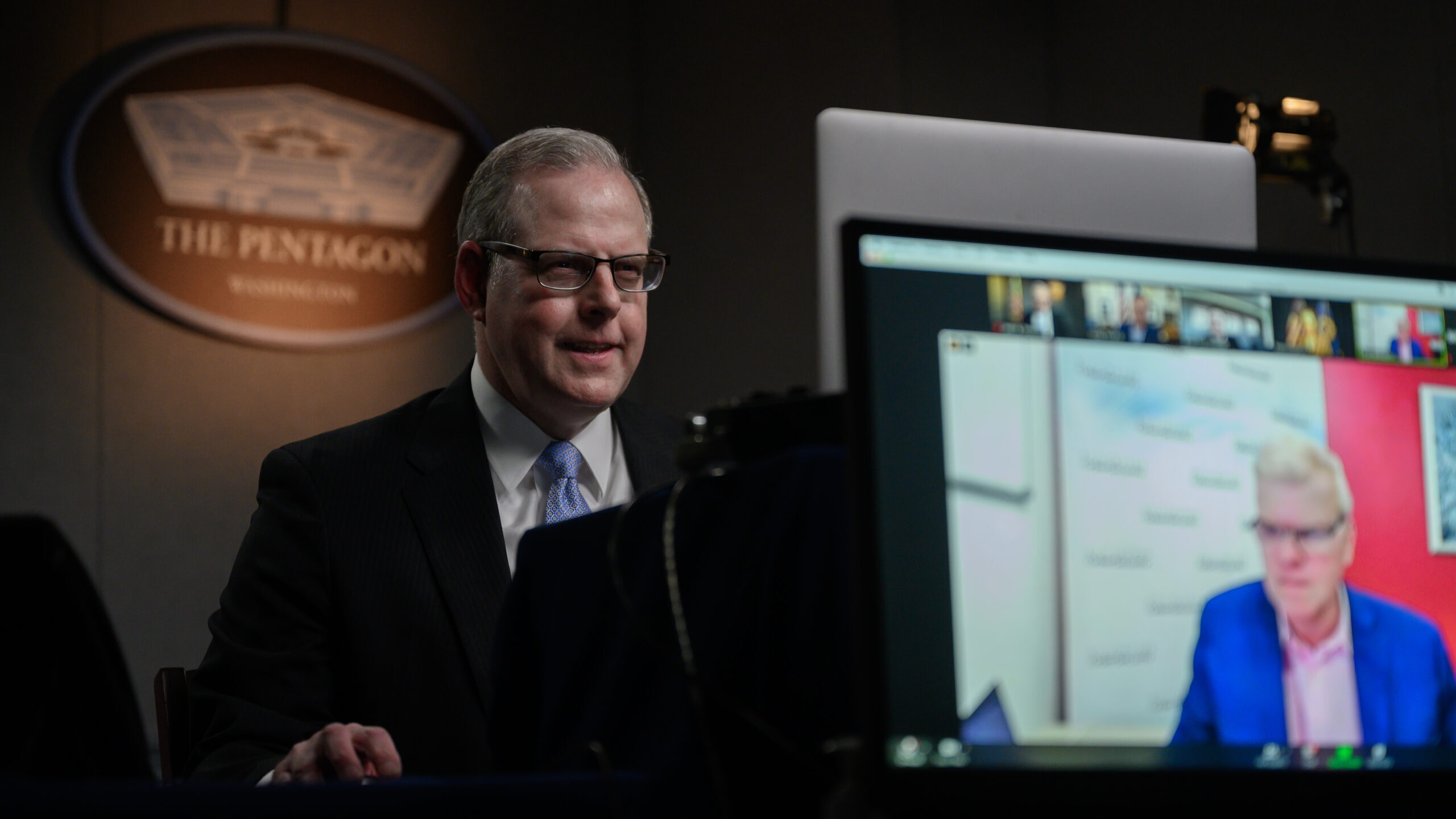
A leak from a “trusted insider who has gone through the background investigation” and been given access to top-secret level capabilities is “a tough one that we have to be able to put measures to get after,” DoD CIO John Sherman said.
By Jaspreet Gill
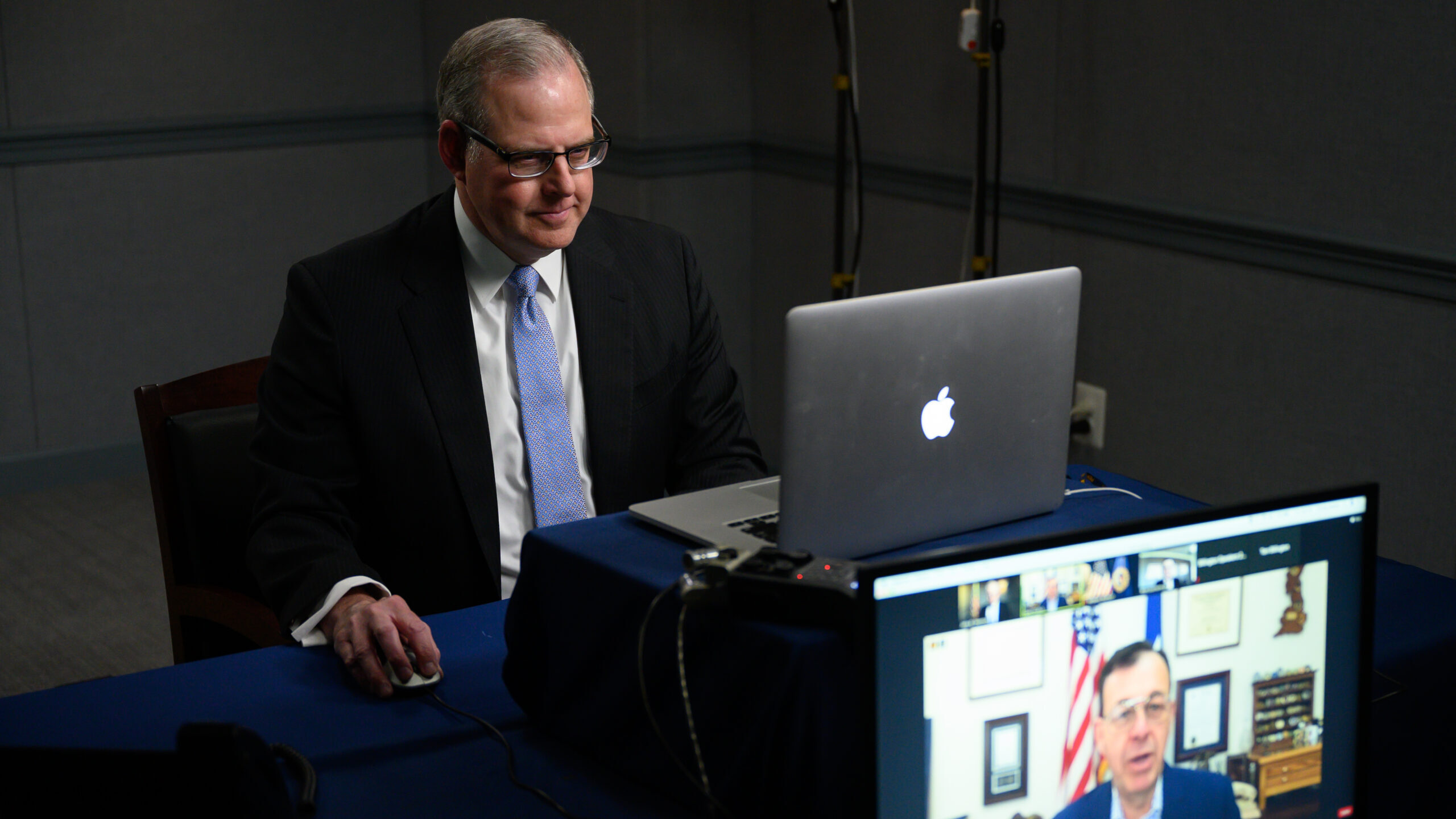
The review, whose initial findings are due in 45 days, involves DoD CIO John Sherman, who’s already been long at work revamping how the Pentagon protects its secrets.
By Ashley Roque and Jaspreet Gill
“Now is the time to drive the dramatic change necessary to make cyber threats far more difficult and far more costly for our adversaries,” DoD CIO John Sherman told Breaking Defense.
By Jaspreet Gill
“That’s a capability we really don’t have in the department – an enterprise top secret cloud environment,” DISA’s Sharon Woods said.
By Jaspreet Gill
“Everyone recognizes our shortages and our problem,” Mike Gorak said. “So we’re going to try new things and we’re going to try innovative things, which, not all will work. and that’s okay.”
By Jaspreet Gill
“This strategy utilizes four human capital pillars – Identification, Recruitment, Development and Retention – to identify and group cyber workforce challenges,” according to slides.
By Jaspreet Gill
“I’m not gonna do anything capriciously or just with a sledgehammer here,” DoD CIO John Sherman said, as he seeks to “make sure the government is getting the best value for our dollar and the very best mission outcome.”
By Jaspreet Gill
The report, without “controlled unclassified information” redactions, discusses concerns with major weapons programs from ships to planes to hypersonic missiles.
By Jaspreet Gill, Theresa Hitchens and Justin Katz
The new plan is broken down into three imperatives: integrating data management, automating resource allocation and fusing situational awareness.
By Jaspreet Gill and Theresa Hitchens
“Naysayers will argue that the strategy is five years or more too late, and although they might be correct, the bigger takeaway is that the DoD has found religion on cybersecurity and they are addressing it architecturally, aiming for a lasting and measurable effect,” Eric Noonan, CEO of CyberSheath and former BAE Systems CISO, told Breaking Defense.
By Jaspreet Gill
The strategy outlines 90 capabilities that will get the Pentagon after what it’s calling targeted zero trust and an additional 62 capabilities for a more “advanced” zero trust, David McKeown, DoD CIO for cybersecurity, said.
By Jaspreet Gill
“I can tell you at DoD, we’re taking this very seriously,” DoD CIO John Sherman said. “And we are committed to implementing zero trust at scale for our four-million-person-plus enterprise that we lead.”
By Jaspreet Gill
“So when they come to government, we have to give them the right skills, we have to give them the right experience so that when they’re done Silicon Valley or industry in general is willing to grab them, right?” CDAO Craig Martell said.
By Jaspreet Gill
The CDAO has established a governance working group looking through “40 different foundational documents” that reference pre-existing organizations before the CDAO or other roles and responsibilities the new office will take over, the deputy in charge said Wednesday.
By Jaspreet Gill